Password & SSH Key Management
Robust password management to secure privileged identities & SSH keys.
80% breaches are the result of used or lost stolen credentials.

Discover.Manage.Rotate
Leverage superior discovery capabilities to automate password management across your IT stack.
Embedded Vauting
Self-managed embedded vaulting for easier manageability and advanced security.
Secure SSH Keys
Secure not just passwords. Manage SSH keys.
World Class Feature to Protect Your Dynamic Infrastructure
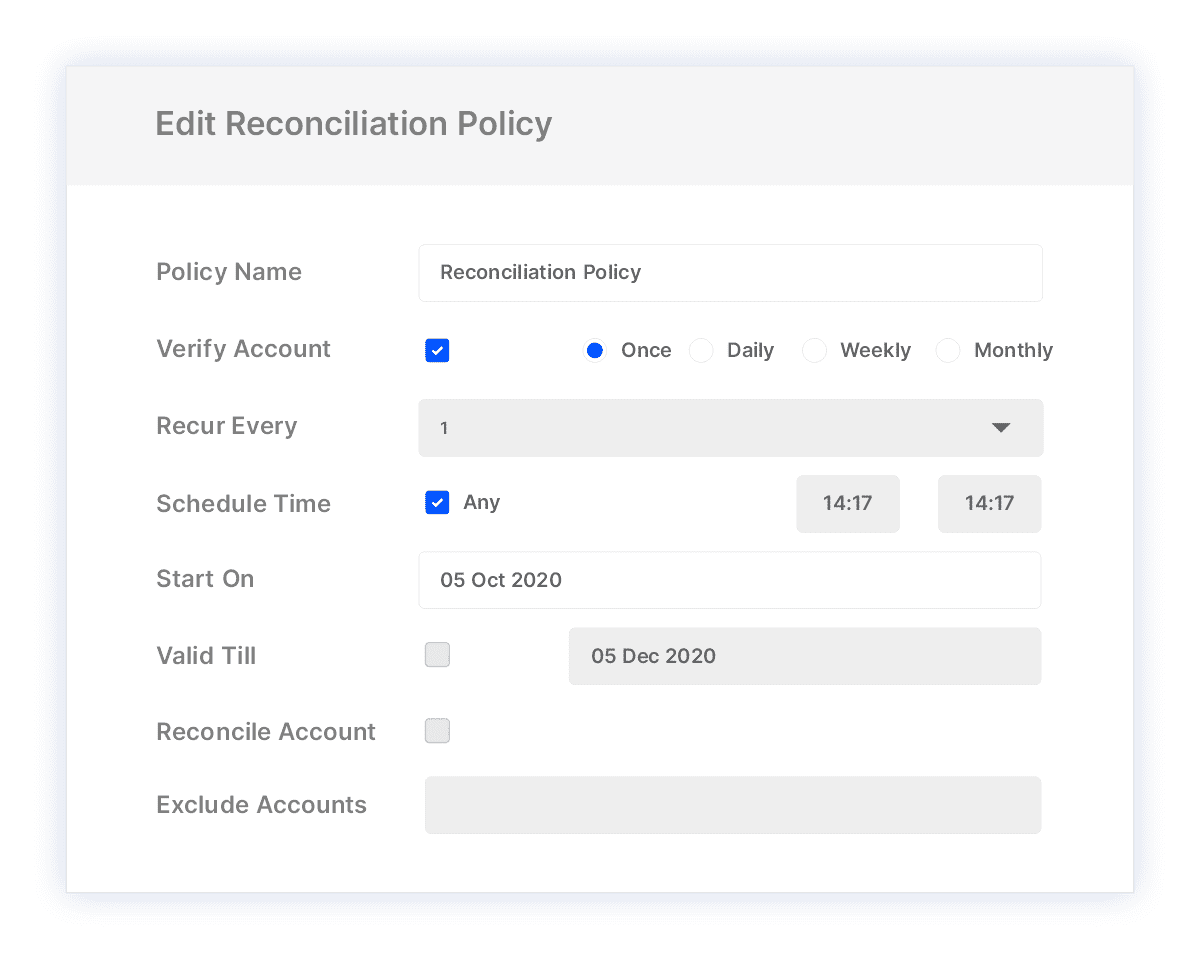
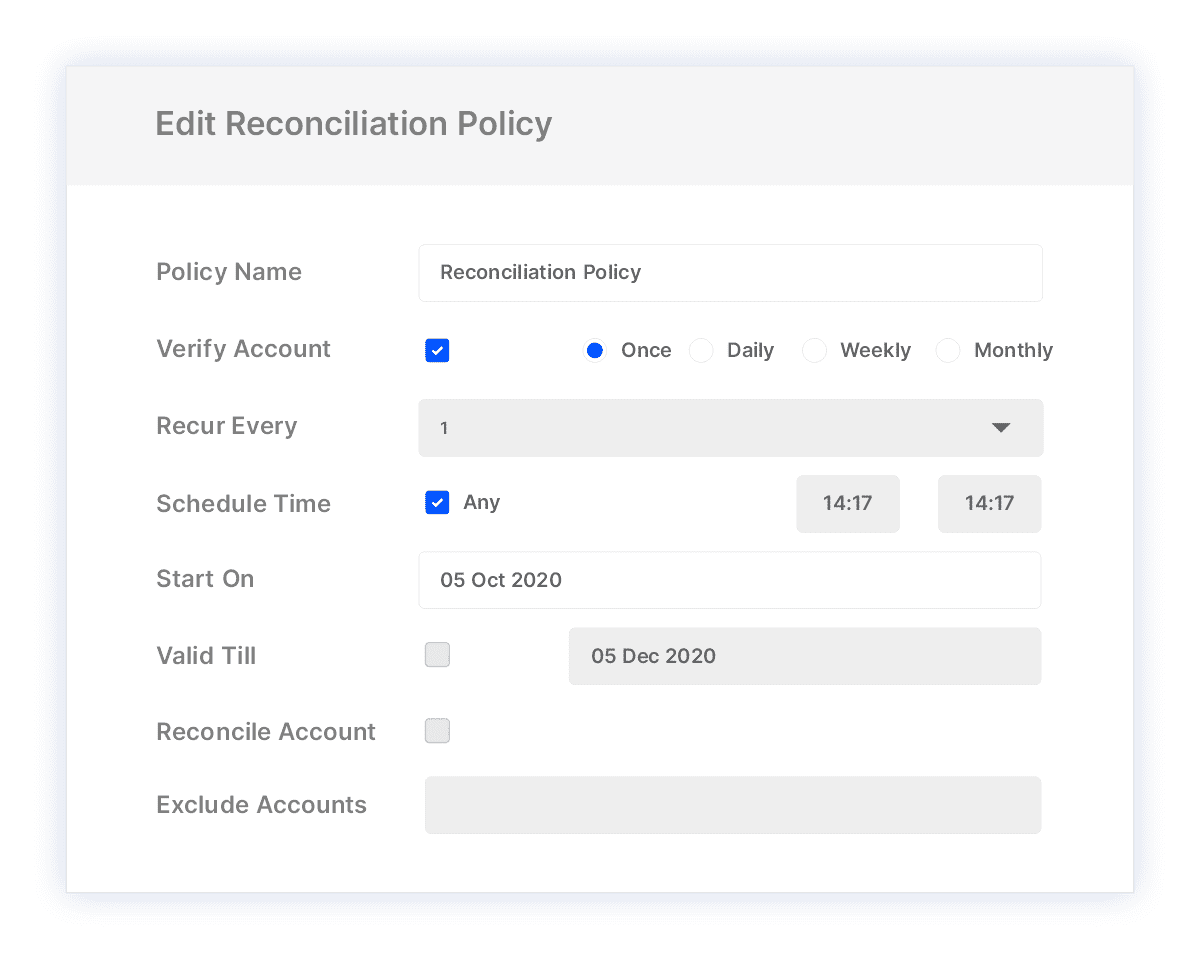
Verify and Reconcile Passwords Automatically
Dynamic infrastructure and fluidic user environments can lead to multiple password checkouts and access requests leading to password exposure risk. Leverage automated password management with periodic verification and reconciliation to reduce risk of password misuse.
Easier Manageability with Dynamic Groups
Simplify policy management for discovered accounts with dynamic groups based on asset types, naming conventions and attributes. Reduce time to onboard accounts and assign access and password management policies.


Easily Build New Connectors
Do more with DIY connector development to rotate passwords for legacy assets or based on your specific needs. Build connectors by leveraging existing protocol connections.
Manage Break-Glass Situations with Satellite Vault
Sync passwords to safe, secure, standalone vaults and retrieve passwords when primary vaults go down or are inaccessible. Satellite vault uses out-of-band authentication available while using same level of security and encryption techniques as primary vaults.




Start Discovering your Assets and Privileged Accounts
Integrations


Why Enterprises Trust Us

Find how 100 yr old bank enhances secure access for safeguarding customer trust.
Read Case StudyExplore the Platform
Achieve more with easy to configure integrated components.
Session Recordings & Threat Analytics
Advanced session monitoring for all privileged activities with risk-profiling & behaviour-based analytics.
Just-in-Time Access
Remove standing privileges and leverage combination of approaches to implement JIT policy.
Privileged Task Management
Reduce risk of excessive privilege by automating & delegating IT operations task.
Account Lifecycle Management
Streamline account provisioning, deprovisioning & operations with complete control.
Windows Privilege Management
Control & secure administrator account usage on your organization’s Windows systems.



