Zero Trust Security Model 101

The current-day IT infrastructure is a combination of local, hybrid and cloud networks with resources and user base spread across the globe. Often, multiple users access sensitive enterprise networks from various locations to perform their jobs. Although this dynamic work culture is crucial for business continuity, it can also expand the attack surface.
It is imperative for businesses to adopt a fool-proof strategy like the Zero Trust Security Model to protect themselves against cyber-attacks. The recent catastrophic security breaches and compromises make it clear that cyber-attacks are inevitable. Threat actors (including insiders) continuously monitor enterprise networks for exploitable vulnerabilities.
In this article, we will discuss some basic concepts pertaining to Zero Trust Security Model, including its basis, importance, and implementation.
What is Zero Trust Security Model?
Zero Trust is a network security framework that relies on continuous authentication and verification of users before providing access to critical enterprise resources. The model goes against the traditional notion of “Trust but Verify.”
Trusting everything inside an organizational setup raises the possibility that threat actors would also be trusted once they get inside a network. In addition, the traditional network security model leverages firewalls and VPNs (Virtual Private Networks) to create a security perimeter – which is a great measure. However, rapid cloud adoption, modern software development practices and hybrid work environments require dynamic security strategies to fight against evolving threats. These strategies can include continuous monitoring, providing least privileges and layered user authentication practices.
With its core principle, “Never Trust Always Verify” Zero Trust focuses on the security of the current modern infrastructure and transformative technologies. In addition, the rapid cloud adoption, software development practices and hybrid work models critically require this security model.
What are the Advantages of the Zero Trust Security Model?
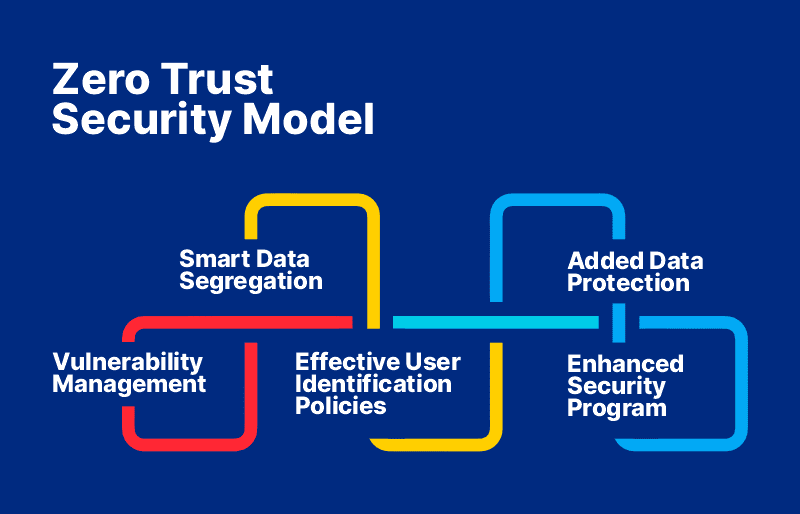
Vulnerability Management
A Zero Trust Security Model protects an organization against lateral risks that might appear inside the network. It reduces the network’s susceptibility to cybersecurity breaches.
Effective User Identification Policies
The Zero Trust model employs Multi-Factor Authentication (MFA) in most situations but sometimes extends beyond passwords to include biometric verification. This method strengthens the security of user accounts. Therefore, strict user identity and access regulations are in place in a Zero Trust environment.
Smart Data Segregation
In Zero Trust Security Model, data is divided depending on the kind, necessity, and sensitivity, of securing the system—this aids in securing sensitive and vital information from intruders.
Added Data Protection
The model safeguards data in storage and in transport. In addition, it utilizes sophisticated capabilities, such as automatic backups as a disaster recovery technique, encrypted or hashed message transmission to protect transferring data, and more.
Enhanced Security System
A Zero Trust Security Model assures that enterprise security strategies work together swiftly and effectively for increased protection. Immediate recovery of inactive security components allows 24/7-failsafe defence.
How to Implement Zero Trust Security Model?
It is true that different organizations need different strategies to implement a comprehensive Zero Trust strategy due to their unique needs. Here, we present one of the logical ways to implement Zero Trust.
- Define the Attack Surface: Securing IT infrastructure that is multifaceted can become a real challenge. Hence, defining the attack surface (e.g., remote devices, public cloud platforms etc.) that needs immediate protection can simplify the challenge of securing a large network at once.
- Segment Network Perimeter into Microsegments and Micro Perimeters: Once the attack surface is defined, micro-segmenting the attack surface can help to prevent lateral movement in case of cyber-attacks. Also, security policy application to micro-segments is simpler and more effective.
- Locate and Catalogue Critical Assets and Applications: Locate all servers, data types, privileged user accounts, third-party vendor who possess access to the IT network.
- Create a Zero Trust Policy: Develop Zero Trust regulations specific to business and access needs and enable role-based access policies. Make sure the policy addresses all concerns about network traffic by asking three basic yet crucial questions:
- Who has access?
- How and when can they access it?
- Where are the resources located?
Especially, focus on privileged accounts that contain critical data and network control.
- Continuously Monitor Network Segments: Zero Trust emphasises on complete network visibility. Businesses must monitor their network to identify active users, traffic flow and verify whether security controls are always implemented. Use tools such as endpoint privilege management, EDR (Endpoint Detection and Response) and SIEM (Security Information & Event Management) solutions to automate the process, reduce human error and efforts.
To Conclude…
Implementing a Zero Trust Security Model and managing its policies without fail may seem daunting from the outside. But, with the right Zero Trust strategy in place, enterprises can reduce their security complexities and increase operational efficiency. Going through each step right from discussing the idea with all stakeholders, aligning team-specific security goals to that of the business, prioritizing action plans and automating each step of the process can help in the long run.
The process increases confidence enabling one to take informed security decisions while also reducing the attack surface. Implementing Zero Trust is also a great way to educate employees on security best practices. And from a network point of view, risks such as unauthorized access, privilege escalation and malware injection can be reduced.
Many organizations have adopted a Privileged Access Management (PAM) solution to address their challenges of securing privileged accounts. A PAM tool can automate mundane yet critical tasks and uphold a few principles of Zero Trust Security Model.



