Password-Based Authentication
Securing the identity and access to a resource through a secret word
What is Password-Based Authentication?
Password-Based Authentication is the process of gaining access to resources to which one is entitled with the help of a set of credentials containing a username and password. This is a rampantly used method known for process simplicity and low cost.
The Need for a Password
In an organisational network, when the control of resources is given to more than one user, the identity of users must be verified and then granted access to their entitlements. That can be done with the help of a password, as it has long been one of the preferred ways to validate one’s identity and relies on one’s ability to authenticate oneself by presenting the correct credential.
Security of all resources in the organisation lies in the complexity and secrecy of the password. If an attacker gets hold of a user’s password, he can impersonate the user and gain access to sensitive resources to which the user is entitled.
Password-Based Authentication is the most preferred method for the majority of resources in the organisation, requiring a username and password. The password-Based Authentication method gets its fondness for its simplicity, cost-effectiveness, ease of operability, and practicality.
Security of all resources in the organisation lies in the complexity and secrecy of the password. If an attacker gets hold of a user’s password, he can impersonate the user and gain access to sensitive resources to which the user is entitled.
Password-Based Authentication is the most preferred method for the majority of resources in the organisation, requiring a username and password. The password-Based Authentication method gets its fondness for its simplicity, cost-effectiveness, ease of operability, and practicality.
How are Passwords Stored?
When a password is created, a copy of that is stored by the website or system in a secure credentials database against which the server would compare further login attempts. In order to avoid a field day for the hackers, it’s imperative that password-based authentication is enabled in encrypted form in a password vault.
What are the Three Types of Authentications?
There are 3 types of authentications:
- Knowledge-based: Also known as “something you know.” This includes traditional passwords. When you, a user, create a unique password for your account, it becomes the key to entering an account repeatedly. It’s something that only the user (hopefully) knows.
- Possession-based: Also known as “something you have.” In this case, an individual verifies themselves using something only they would have. For instance, a user could swipe a physical key card to prove that they are who they claim to be.
- Inheritance-based: Also known as “something you are.” These are biometric characteristics such as a facial scan or a fingerprint that is used to verify an individual’s identity.
Note: Methods like Token-based authentication, Biometric-based authentication, or Key-based authentication are capital-intensive owing to their infrastructure & training requirements. Most service providers, therefore, tend to avoid this complex process and opt for the more straightforward Password-Based Authentication option.
What are Password Alternatives?
Any type of authentication protocol wherein a typical ID and/or key is not used to grant access to users is a password alternative. Password alternatives mostly come under inheritance or possession-based methods.
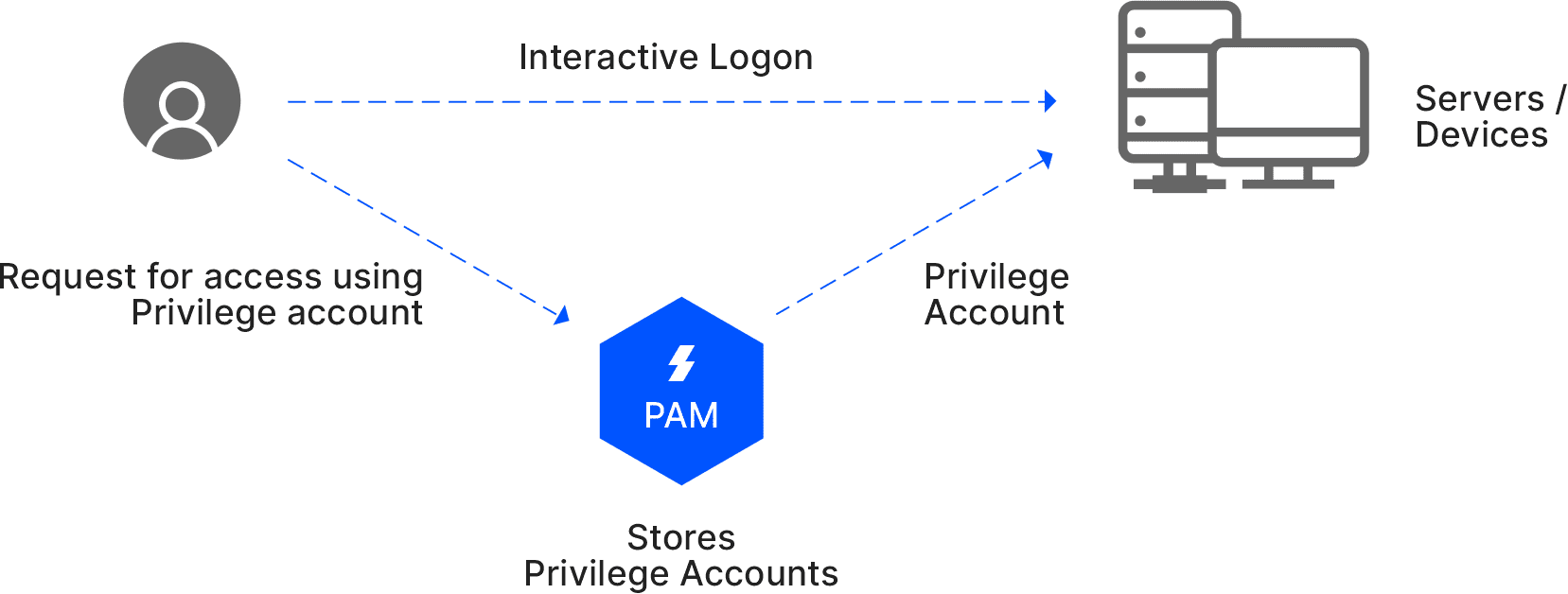
How does Sectona Fulfil this Requirement?
Sectona Security Platform provides an automated Password Management capability that facilitates and easily monitors privileged user access. Organizations can use Sectona PAM tool enable a robust password management to store and secure passwords.
Related Concepts
Was this article helpful?
YesNo