Shared Account and Named Account
Protecting the access to the accounts and their delegated entitlements
Defining a Shared Account: –
An account which allows multiple users to access resources using a single set of credentials and can be used across any platform, network or database is called a Shared Account. Shared Accounts can either be a Privileged account or a Generic Non-Privileged Account.
Privileged accounts can be either Administrator/Root accounts (accounts created by administrator for privileged activities) or Default Accounts present on all systems built-in, which are by default shared accounts utilized by multiple admins to delegate and perform administrative action on the resource.
A Generic Non-Privileged Account is created at the infrastructure level for business users so that they can connect with the database or the server hardware and carry out the delegated tasks they are entitled to act on.
Defining a Named Account: –
An account delegated to a user who can access multiple resources he/she is entitled to with the same account is called a Named Account. A named account can either be a privileged account or a non-privileged account. Always created on the infrastructure level, each account is attributed only to a single user. Each named account is also used for validating the identity of the user when he/she intends to access a resource.
Sectona PAM Solution: –
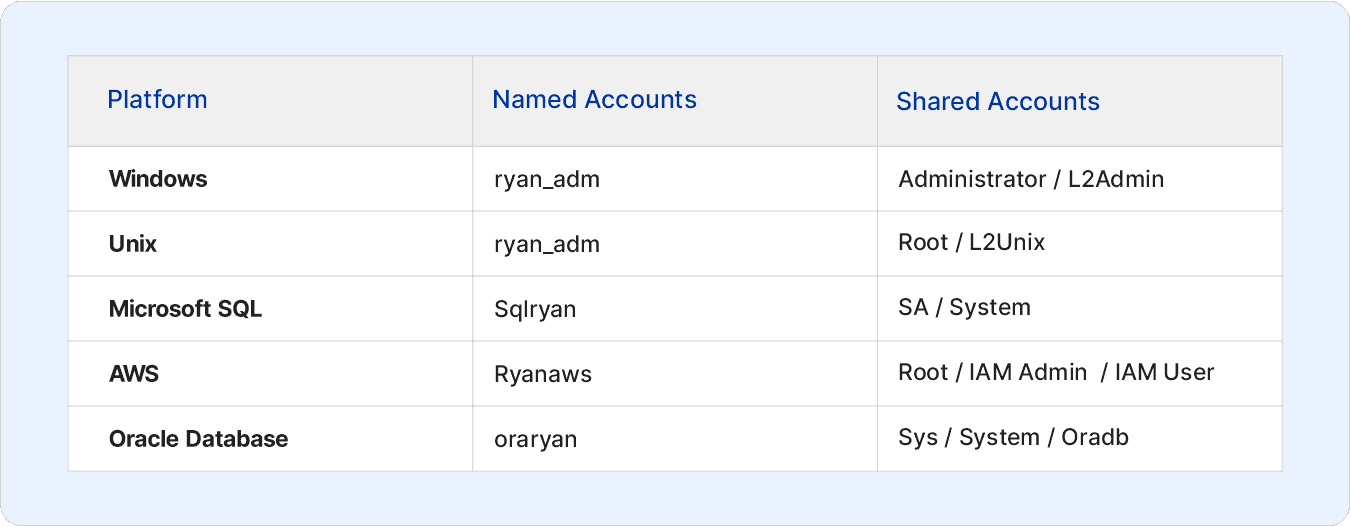
Sectona’s Privileged Access Management solution facilitates secure access to both shared and named accounts to de-risk and safeguard such set of accounts from misuse or credential theft. With Sectona PAM, accountability can be associated with the usage of any shared or named privileged accounts for improved governance and audit. Below is a preview of different types of accounts associated with different platforms referenced according to their designated nomenclature.